Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Not-So-Hidden Cost of Unpatched Devices
A patch management strategy that considers the risks, prioritizes critical patches and ensures timely deployment will reduce business disruptions, improve operational efficiency and create a competitive advantage.
Understanding and Preventing Ransomware Attacks
Understanding ransomware attacks is the first step in being able to prevent them from successfully targeting an organization. To prevent ransomware attacks, organizations must have strong security protocols in place such as performing regular system backups and training employees to avoid social engineering scams, among other measures. Continue reading to learn more about ransomware attacks and what organizations can do to stay protected against this type of attack.
Datadog acquires Codiga
Developers spend over a third of their time fixing bad code and reducing technical debt. Detecting and fixing errors in production is not only more costly than doing so during development but also slows down innovation and has a negative impact on productivity, the development experience, and team morale. Having tools that help catch and fix coding mistakes earlier in the development process creates a better experience and increased productivity.
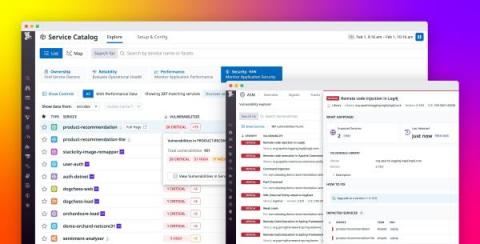
Gain visibility into open source vulnerabilities with Datadog Application Vulnerability Management
Open source libraries have become an indispensable part of modern applications. Approximately 90 percent of organizations use open source software to support their services, but monitoring these dependencies can be difficult when environments run thousands of ephemeral services.
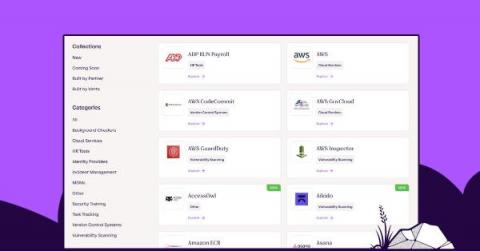
Vanta delivers over 50 new integrations in one quarter
We’re thrilled to announce that we’ve delivered more than 50 new system integrations over the past quarter, taking us to a total of 110 integrations. This is far ahead of any other automated compliance solution in the market, reflecting our innovation velocity and long-term commitment to ensuring customer value and success with Vanta.
DevOps Midwest - A community event full of DevSecOps best practices.
DevOps Midwest 2023 brought together experts in scale, availability, and security best practices. Read some of the highlights from this DevSecOps-focused event.
Behind the Curtain: Falcon OverWatch Hunting Leads Explained
Most hunting enthusiasts agree that the thrill of hunting lies in the chase. Equipped with experience and tools of their trade, hunters skillfully search for signs of prey — a broken twig, a track in the mud. CrowdStrike® Falcon OverWatch™ threat hunters are no different. They search for signs of their prey — of adversaries lurking in the dark — and these signs are called hunting leads.
Cyber Essentials 2023 update
This month, the NCSC and its Cyber Essentials delivery partner IASME will update the technical requirements for the 2023 Cyber Essentials scheme. These changes come as part of a regular review of the scheme’s technical controls, ensuring that it continues to help UK organisations guard against the most common cyber threats. Changes come into play on 24th April 2023, and as stated on their website, these modifications will cover a variety of key areas.
Deceptive 'Vibranced' npm Package Discovered Masquerading as Popular 'Colors' Package
A new malicious package has been detected on the Node Package Manager (npm) repository that poses a significant threat to users who may unknowingly install it. Named ‘Vibranced,’ the package has been carefully crafted to mimic the popular ‘colors’ package, which has over 20 million weekly downloads.