Making Cyber Risk Intelligence Easier to Understand, Explain, and Act On
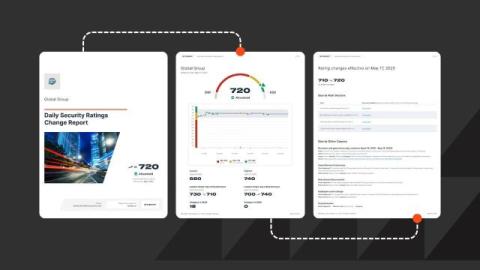
Helping customers understand rating changes has always been a core commitment at Bitsight. A rating shift can spark questions from executives, board members, or regulators, and security leaders must be ready to answer with clarity and confidence. That’s why we’ve introduced new updates to the Bitsight platform designed to make our cyber risk intelligence solutions more actionable.