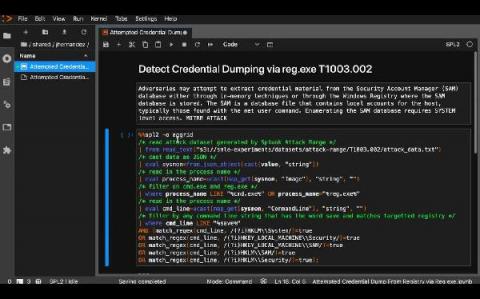
Detecting HAFNIUM Exchange Server Zero-Day Activity in Splunk
If you want just to see how to find HAFNIUM Exchange Zero-Day Activity, skip down to the “detections” sections. Otherwise, read on for a quick breakdown of what happened, how to detect it, and MITRE ATT&CK mappings.