Amazon SES monitoring: Detect phishing campaigns in the cloud
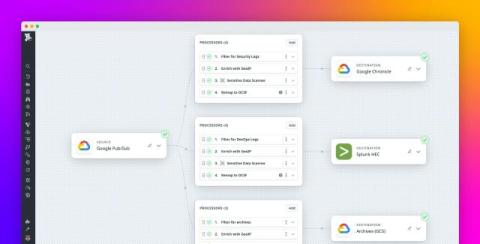
Amazon Simple Email Service (Amazon SES) is a cloud-based provider for sending transactional, marketing, and newsletter emails. Because of its role as a source of communication for organizations, Amazon SES has become a primary tool for phishing campaigns. Our latest threat roundup includes a key finding that Amazon SES is a common target in the initial stages of a cloud control plane attack.