Introducing Vulnerability Management Enhancements for Sysdig Secure: Focus on Action
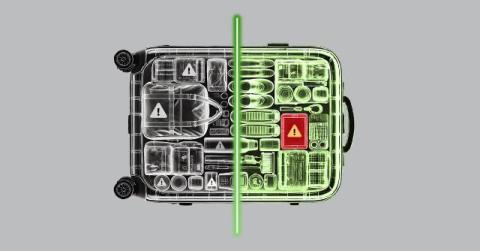
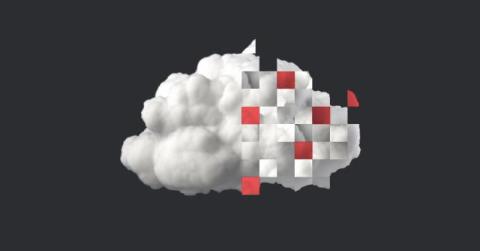
Vulnerability management in the cloud is more challenging than ever. Security teams are drowning in vulnerability alerts, asked to deal with them quickly even as the list continues to expand. What they lack is a clear path to remediation. Legacy tools flood teams with critical alerts, while offering little guidance on which fixes will be most impactful. Vulnerability management isn’t just about identifying the biggest risks — it’s about taking decisive action.