Wireshark: Ethereal Network Analysis for the Cloud SOC
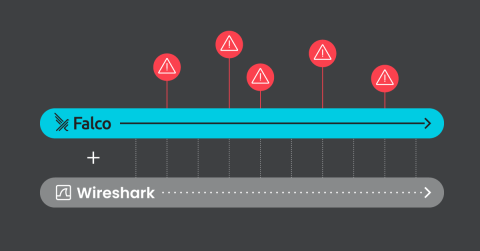
Remember Wireshark from the good old days of your IT degree or early engineering adventures? Well, guess what? It’s still kicking and just as relevant today as it was back then, and guess what else? It is still open source! Do your engineering or security teams use it? There’s a good chance they do if you’re on-premises. Believe it or not, Wireshark isn’t just for the land of wires and cables anymore. With some help from Falco and Kubernetes, it has a place in the cloud SOC.