Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How Passwordless Works
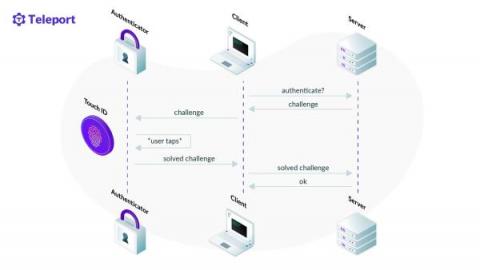
Passwordless is a form of authentication that doesn't require users to provide passwords during login. That much you could glimpse from the name, but how does it work? What are its trade-offs? This blog post will do its best to explain to you how passwordless can be implemented using modern technologies such as Web Authentication (WebAuthn), while at the same time providing better user experience and security than the traditional password-based approach.
Creating a .gitignore file - How we can use git ignore to prevent adding unwanted files to git
What You Need to Know About Fine-Grained vs. Coarse-Grained Authorization
With the growing importance of cloud-native security and zero-trust approaches to software, questions around the level of access granted to cloud resources have become more critical. Equally important is to understand the value of different authorization strategies. In this article, we present an overview of fine-grained and coarse-grained authorization methods.
Using XACML with OPA and Rego: The Best of Both Worlds
XACML is an OASIS standard for implementing declarative authorization policy. It was intended to be a widely adopted technology that would move authorization policy decisions out of application code and into a specialized Policy Decision Point (PDP). The terms often used in the OPA world, such as PDP, PIP (Policy Information Point) and PEP (Policy Enforcement Point) all come from the XACML standard. You can read more about XACML in Anders Ecknert’s blog post on architecting authorization.
Today's Security Tidbit: An Encrypted JSON File Containing Malicious Code
As security researchers, we see new malicious methods being introduced on a daily basis from the ever-industrious global cadre of malicious actors. But not all of the things we find constitute breaking news. Sometimes, we run across something that doesn’t necessarily pose a threat, but still piques our interest. Instead of being the security equivalent of a four-course meal, it’s more of an amuse bouche.
How to Secure Redis
Redis is an in-memory data store that stores data in key-value pairs. It’s primarily used as a cache for quick data access, as a database, and as a message broker. Redis doesn’t have a default authentication setup in place exposing it to security vulnerabilities, which if exploited could potentially affect the infrastructure of the entire organization. These security vulnerabilities are what make securing your Redis database so important.
The Developer's Guide to a Seamless Kubernetes Deployment
To grasp the concept of a Kubernetes Deployment and Kubernetes Deployment strategy, let’s begin by explaining the two different meanings of the term “deployment” in a Kubernetes environment: Kubernetes Deployment allows you to make declarative updates for pods and ReplicaSets. You can define a desired state and the Deployment Controller will continuously deploy new pod instances to change the current state to the desired state at a controlled rate.
Granular and Seamless Just-in-Time (JIT) Access with Teleport
As software companies grow, they start to see exponential growth in resources needed to support the business. A startup can quickly go from a few servers and a handful of databases to a sea of Kubernetes clusters. Managing access to all of these resources comes with a myriad of problems. One problem at scale is deciding who can access what resources and how to provide relevant access to those resources on-demand.
Testing effectively in Terraform
Terraform is an infrastructure as code (IaC) solution that enables DevOps teams to use coding concepts to automatically deploy on-premise or public cloud infrastructure components. These components may include virtual machines, network components, storage, applications, or database services. Terraform provides HashiCorp Language (HCL).