Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Customer Corner: "How BigCommerce Achieved Real-Time Cloud Security"
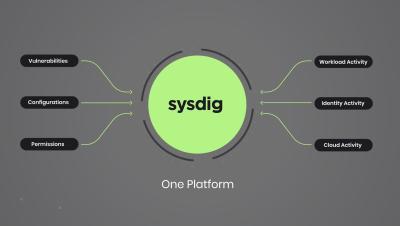
Rethinking Cloud Security with Sysdig's CNAPP
Unlock the Power of Google Chronicle SIEM for Your Clients
Let's face it: Managing cybersecurity for multiple clients as an MSP can feel like navigating a maze, full of pitfalls and traps. Just when you think you have one security issue managed, another one pops up.
New Study Reveals Cloud Giants are Holding Businesses Captive
Welcome to connectivity cloud: the modern way to connect and protect your clouds, networks, applications and users
The best part of our job is the time we spend talking to Cloudflare customers. We always learn something new and interesting about their IT and security challenges. In recent years, something about those conversations has changed. More and more, the biggest challenge customers tell us about isn’t something that’s easy to define. And it’s definitely not something you can address with an individual product or feature.
Cloudflare One - Secure Web Gateway
Ensuring vendor integrity: Why the cloud shouldn't be your only backup
As a senior consultant I deal with customers across numerous industries and maturity levels. I am often engaged in conducting risk assessments or gap analysis aligned with common frameworks such as the National Institute for Standards and Technology’s (NIST) Cybersecurity Framework (CSF). Most, if not all, the frameworks have a few controls that focus on the organization’s backup processes and disaster recovery plans.
Cloudflare account permissions, how to use them, and best practices
In the dynamic landscape of modern web applications and organizations, access control is critical. Defining who can do what within your Cloudflare account ensures security and efficient workflow management.
Ensuring Compliance in an Ever-Evolving Cloud Security Landscape
According to CSO the fines incurred for data breaches or non-compliance with security and privacy laws, for only a handful of companies, has cost $4.4 billion. The global average cost of a data breach in 2023 was $4.45 million, a 15% increase over 3 years (IBM). The challenge for organizations is how to safeguard sensitive information while adhering to the law, but without compromising innovation. Cyber threats loom large, affecting businesses in every industry.