Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to use AWS and Vanta for identity and access management
This blog is part of a series about how to use Vanta and AWS to simplify your organization’s cloud security. To learn more about how to use Vanta and AWS, watch our Coffee and Compliance on-demand webinar. Amazon Web Services, or AWS, is one of the most popular cloud providers for organizations today — providing one of the most flexible and secure cloud environments available.
Introducing Cloudflare's 2024 API security and management report
You may know Cloudflare as the company powering nearly 20% of the web. But powering and protecting websites and static content is only a fraction of what we do. In fact, well over half of the dynamic traffic on our network consists not of web pages, but of Application Programming Interface (API) traffic — the plumbing that makes technology work.
Harnessing the Power of the Cloud: Understanding the Vital Role of Privileged Access Management
Understanding Six Popular Azure Storage Types and Their Use Cases
The modern enterprise is all about the cloud. Digital transformation includes not only the adoption of cloud computing through application migration, but a transition from disk storage to cloud storage. Cloud storage has some key advantages over traditional disk storage, including the following: While there are multiple cloud storage options available today, including Amazon Web Services (AWS), Azure Storage is a logical choice for Microsoft Azure customers.
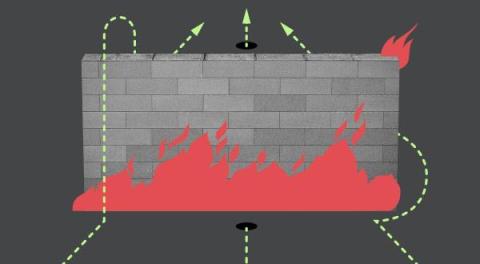
DDoS threat report for 2023 Q4
Welcome to the sixteenth edition of Cloudflare’s DDoS Threat Report. This edition covers DDoS trends and key findings for the fourth and final quarter of the year 2023, complete with a review of major trends throughout the year.
Escape Python's Stranglehold With AWS CLI
Escape Python's Stranglehold With AWS CLI
Mitigating cloud security risks through comprehensive automated solutions
A recent news article from Bleeping Computer called out an incident involving Japanese game developer Ateam, in which a misconfiguration in Google Drive led to the potential exposure of sensitive information for nearly one million individuals over a period of six years and eight months. Such incidents highlight the critical importance of securing cloud services to prevent data breaches.
Privacy Pass: Upgrading to the latest protocol version
The challenge of telling humans and bots apart is almost as old as the web itself. From online ticket vendors to dating apps, to ecommerce and finance — there are many legitimate reasons why you'd want to know if it's a person or a machine knocking on the front door of your website. Unfortunately, the tools for the web have traditionally been clunky and sometimes involved a bad user experience.