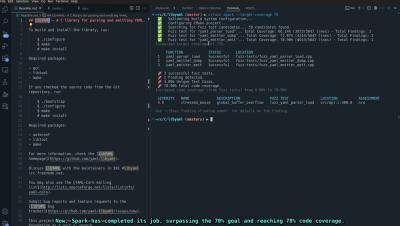
Spark Demo: Code Intelligent's AI Test Agent
Demo: AI Test Agent in Action Discover the benefits of CI Fuzz 2.0, our powerful tool that simplifies fuzzing to a single command. The demo will also highlight root cause analysis capabilities, showcasing how vulnerabilities can be identified and addressed efficiently, this demo will uncover several real-world severe vulnerabilities uncovered by AI Test Agent in widely used open-source libraries during the past few months.