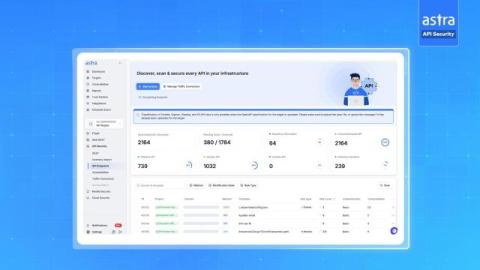
This API Security Mistake Could RUIN Your Business #apitesting #hacking_or_secutiy #apisecurity
Testing your APIs after deployment is one of the biggest mistakes teams make. By the time vulnerabilities are discovered in production, the risk is higher, fixes take longer, and attackers may already exploit them. In this short clip from our API Security webinar, we explain why “shift-left” testing — securing APIs before deployment — is critical to prevent breaches.