Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
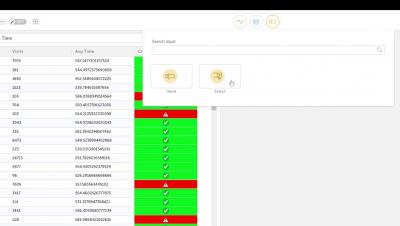
Activeboard [3] - Variable data
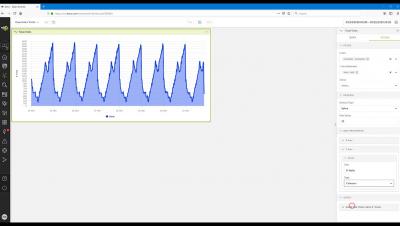
Activeboards [4] - Creating a Line Chart Widget
To Air-Gap or Not Air-Gap Industrial Control Networks
What camp are you in? In the camp that believes in air-gaps, or the other set that says they truly do not exist? Air-gap networks are networks that are physically and logically isolated from other networks where communication between these networks is not physically or logically possible.
How to use Teramind to monitor and block data exfiltration attempts to USB/external drives
Adding to the Toolkit - Some Useful Tools for Cloud Security
With more business applications moving to the cloud, the ability to assess network behavior has changed from a primarily systems administration function to a daily security operations concern. And whilst sec-ops teams are already familiar with firewall and network device log tools, these can be of limited used in a “cloud first” business where much of the good traffic that occurs is hard to distinguish from potentially risky traffic.
Climbing the Vulnerability Management Mountain
The purpose of this series of blogs is to guide you on your journey up the Vulnerability Management Mountain (VMM). Like climbing a mountain, there is a lot of planning and work required, but when you get to the top, the view is amazing and well worth the journey. Your progress will depend on your funding and priorities, but climbing at a quick steady pace will help secure your environment.
HTTP response splitting exploitations and mitigations
HTTP Response Splitting is a type of attack that occurs when an attacker can manipulate the response headers that will be interpreted by the client. This article goes into details on how this can be abused by an attacker to insert arbitrary headers and the impact of this type of attack.
Weekly Cyber Security News 14/06/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. Privacy is understandably a concern for all, and for those that are not that bothered and opt-in to give it away, I’m sure they assume it is for monitoring of their activities online. However, in this enterprising case, it appears to go beyond the virtual to physical and not where you would suspect…