Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
How Will the CMMC Impact My Business and How Can We Prepare? Part 3 of 3
The CMMC enforcement model will require a significant adjustment to the way contractors conduct government business – from procurement to execution. In Part 2 of this series, I discussed the possible impacts of having your company’s security rating made public. In Part 3, I would like to discuss the impact of having one unified standard for cybersecurity on a company’s compliance practices.
Revisiting and Revising Some Tips for National Cyber Security Awareness Month
As a regular reader of Tripwire, you are aware that October is National Cyber Security Awareness Month. Way back in 2015, when the world was an entirely different place, I contributed an article that offered some tips for protecting yourself. Since that article, other scams have taken a front seat towards compromising our security. They are not new, but they seem to be the new “flavor of the day.”
11 Respected Providers of IT Security Training
We at The State of Security are committed to helping aspiring information security professionals reach their full potential. Towards that end, we compiled a list of the top 10 highest paying jobs in the industry. We even highlighted the U.S. cities that tend to reward security personnel with the best salaries, amenities and other benefits. Knowing which job title you’d like and where you’d like to live goes a long way towards advancing one’s infosec career.
Cyber Threats to Medical Imaging Systems and How to Address Them
Healthcare continues to see staggering growth in breaches to patient health information. In the first half of 2019 alone, 32 million health records were breached, compared to 15 million records in the entire year of 2018. However, this trend of growing cyber breaches in healthcare is likely to persist due to the following characteristics of the healthcare industry...
What are the Five Components of Information Security?
Information security covers a wide area of various practices and techniques. In this article, we will take a closer look at the main components of this field.
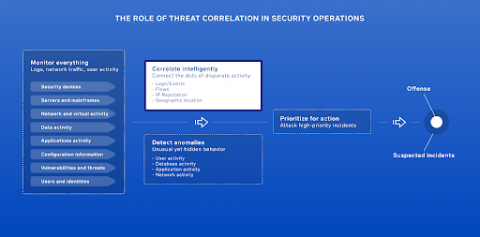
Why security monitoring falls short and what can be done about it
There are parts of every business considered to be critical to its ability to function. Email, accounting, and customer service are a few. Indeed, if email went down, accounts receivable stopped, or customers couldn’t talk to anyone, the business would suffer. There is another critical function of business that isn’t widely viewed as such: security monitoring.
Weekly Cyber Security News 27/09/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. Three surprises this week with the first, well, I don’t think any kind of lead in will help. Just go for it, it’s a crazy one...
What is Phishing?
Phishing is a cyber attack that gathers sensitive information like login credentials, credit card numbers, bank account numbers or other financial information by masquerading as a legitimate site. Personal information like social security numbers, phone numbers and social media account information are also common targets for cybercriminals who perform identity theft. Phishing scams trick victims by using social engineering to create a sense of urgency.
What is Threat Hunting?
If you are involved in the cyber security processes, you must have heard of the term threat hunting. In this article, we discussed this rather popular concept in detail. Being one of the buzzing concepts of cyber security, threat hunting has been increasingly popular, but what does it refer to? Do you need it? Should you be doing it? We will answer all these questions in detail.