Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Undivided we fall: decoupling network segmentation from micro-segmentation in the software defined perimeter
As of today, no laws or regulations, even the latest version of PCI-DSS, HIPAA, and HITECH, do not make network segmentation or micro-segmentation compulsory to comply with the rule. By making network segmentation discretionary -- even when transmitting, processing, or storing regulated data, the number of breaches will continue to rise as companies err on the side of doing less with more.
Reimagine Your Perimeter
The Netskope Security Cloud: Your New Perimeter
Best Practices for Using Tripwire Enterprise in Dynamic Environments - Part 1
Just a few years ago, most IT environments were made up of deployed servers on which personnel installed applications, oftentimes as many as that one system could handle. They then remained and ran that way for years. In the meantime, the IT team maintained the system and updated the applications as needed. Sometimes there were test versions of those systems, but this wasn’t often. Even then, the OS often didn’t match the production version of the same system.
SIEM Deployment Checklist
SIEM deployment process can be rather involved and overwhelming since SIEM can offer a wide array of solutions for different needs of your organization. In this blog post, we discussed the deployment process of SIEM and added a brief checklist. SIEM tools have been one of the most topical tools in the industry for a while now. They offer a wide range of solutions to organizations from various backgrounds and sectors.
Disturbing Cybersecurity Trends In Aviation
Aviation is a component of critical infrastructure that is comprised of a complex web of public and private organizations relying on millions of assets to move people and cargo around the world. The industry supports countless critical functions such as emergency response, community access, agricultural support, passenger services, national security, law enforcement, border security, intermodal connections to rail and shipping, and much more.
Medical apps & privacy: where are we?
Image Source: Unsplash Finding a new health-related app that tracks symptoms, increases self-care behaviors, or offers disease-specific education can be exciting for consumers. However, many apps share information with a host of other companies for marketing purposes. Often, these companies have nothing to do with healthcare and are not even a business the individual uses.
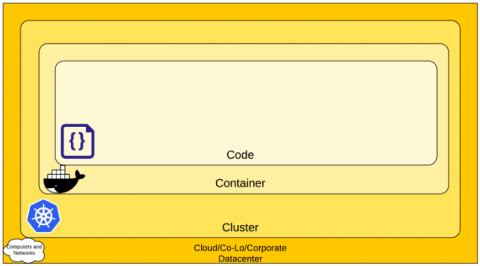
How to Secure Kubernetes Using Cloud SIEM?
The Top 10 Highest Paying Jobs in Information Security - Part 2
Information security is an exciting and rapidly growing field for individuals who are interested in protecting users and their data. In an effort to map out the industry as a possible career choice, we recently conducted research into the top 10 infosec jobs based on overall pay grade. We now continue with the second part of our two-part series.