Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Preventing 'Unlimited' ATM Cash-out Attacks
Malware Analysis for Threat Hunting
Malware analysis allows the analyst to see what actions are taken and allows us to use those actions to build a profile that can be used to detect and block further infections and find related infections.
Cross-site scripting (XSS) explained
Analyzing Website Visits
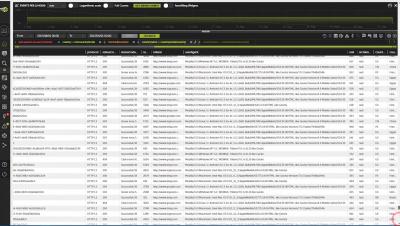
Enhancing Streaming Data with Devo
Why Security Configuration Management (SCM) Matters
In the Godfather Part II, Michael Corleone says, “There are many things my father taught me here in this room. He taught me: keep your friends close, but your enemies closer.” This lesson Vito Corleone taught his son Michael is just as applicable to IT security configuration management (SCM).
Devo Selected to the "GSMA 100"
5 September 2018, Cambridge, Mass: Devo Technology today announced that it has been named one of the first companies in the “GSMA 100,” a global innovation discovery initiative developed by the GSMA to identify and advance the next generation of connectivity and digital services.
XSS using quirky implementations of ACME http-01
TL;DR Some hosting providers implemented http-01 having one part of the challenge key reflected in the response. This resulted in a huge amount of websites being vulnerable to XSS just because of their implementation of the http-01 ACME-challenge.
How Trade Secrets Can Be Abused By An Attacker After A Data Breach
Even as public awareness of data breaches grows, the popular conception of what information is sensitive, and how sensitive it is, lags behind the threats that individuals, businesses, and governments face today. The classic model for a data breach is individuals’ login credentials for banking or private identity information like their social security numbers, but there is equal– and in many cases far greater– value in information with less obvious potential for abuse.