Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
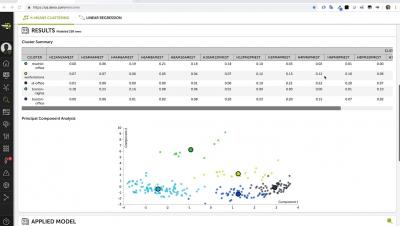
Devo Machine Learning - Quick Modeler K-Means Clustering Example
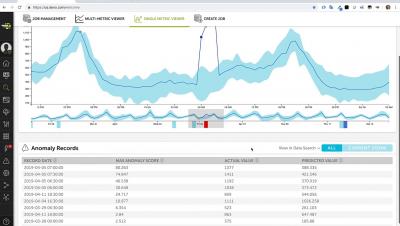
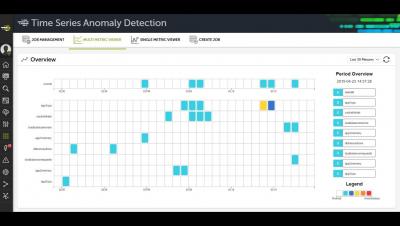
Devo Multi-metric Time Series Anomaly Detection
Docker and Kubernetes in high security environments
Container orchestration and cloud-native computing has gained lots of traction the recent years. The adoption has increased to such level that even enterprises in finance, banking and the public sector are interested. Compared to other businesses they differ by having extensive requirements on information security and IT security. One important aspect is how containers could be used in production environments while maintaining system separation between applications.
Data-first Culture + Employees = Better CX
There’s a lot of talk about the ability of AI and machine learning to augment digital transformation journeys by creating better customer experiences and empowering employees to make decisions using data. However, IT and business leaders can sometimes face analysis paralysis when confronted with this topic because it means something different for every business – and it means shifting an entire company culture towards a new way of working. One key shift is making use of machine data.
Importance of Cybersecurity and The Role of SIEM and SOAR
These days the word ‘intelligence’ pops up in any conversation on security. Why is the industry cannot get enough of it? What is the difference between intelligence and information? What is intelligence-led security? Let’s take a look.
How to build a home IT security lab: Episode 1
Hello all and welcome to the first episode of a new blog series focused on how to prevent WordPress site hacks. In this first post of the series, I will provide videos and articles that will comprise a set of tutorials to show you the ins and outs of building a home lab that will give you the flexibility to test, hack, or learn just about anything in IT.
Detectify Crowdsource | Meet the Hacker - Linus Särud
Fitting automated security throughout the CI/CD pipeline
As companies compete with how fast new features and products can be released on the digital market, a byproduct of DevOps could be the neglect of sufficient and consistent information security throughout the pipeline – yes that means from start to the next improvement. Sure, automated security testing in production is a given, but what about during build and testing in the Continuous Integration and Continuous Delivery (CI/CD) Pipeline?