Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Remote Work Endpoint Management Security Challenges
Cybersecurity challenges of the work-from-home model
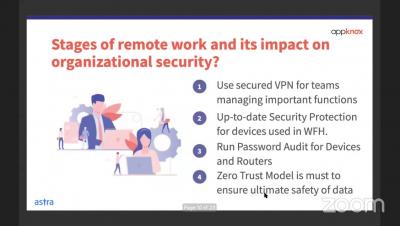
Just recently, the World Health Organization declared coronavirus a global pandemic. This decision brought with it several health and safety measures, and normal life came to a halt in many countries. This resulted in many organizations around the world adopting telecommuting methods to prevent the spread of COVID-19. While people are adjusting to the sudden changes in the way they work, cybercriminals are using this opportunity to exploit new vulnerabilities the work-from-home environment presents.
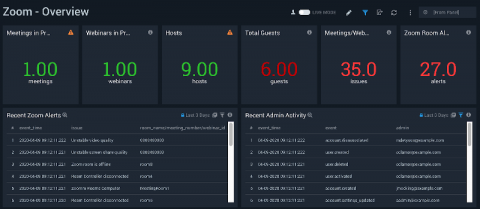
Ensure a secure and reliable Zoom video conferencing service
Cybersecurity in Education (K-12) with the CIS Controls
Acknowledging recent reports of ransomware targeting educational institutions, it is no wonder that there have also been articles that attempt to lure in readers with “free” tools. What is disappointing is that these “free” tools are little more than marketing pieces that direct you to click on readily available documentation from Microsoft or Google.
Insider Data Theft: Definition, Common Scenarios, and Prevention Tips
People tend to trust those they work with: employees, business partners, subcontractors. But these people, who have access to all kinds of corporate data, don’t always prove worthy of such trust. Insider data theft statistics show that one in four employees won’t think twice before stealing sensitive data from their current company if it will help them sign a contract with a competitor.
How Do DDOS Attacks Work?
DDoS attacks are considered as one of the most popular cyber-attacks and they have the ability to make systems go down for a very long time. Read more to learn how they work and how you can stop them. What is a DDoS attack? DDoS attack (also known as the distributed denial of service attack) is a dangerous and common type of cyber-attacks. It aims to overwhelm the target through disrupting the regular traffic of a service, network or a server.
Five worthy reads: Keeping a close eye on cybersecurity while working remotely
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we highlight the importance of creating and enforcing a solid cybersecurity strategy for employees who work remotely.
Computer Forensic Tools - Providing The Evidence You Need
If you are even considering investigating an employee or monitoring employees in general, consider modern computer forensic tools for a complete solution. Computer forensic tools allow an employer to gather digital evidence before confronting an employee. With the Covid-19 (Coronavirus) outbreak, these types of solutions can also help to monitor employees that are self-quarantined or voluntarily working from home.
Assess and adapt for resiliency
Admittedly, we are in uncharted territory – what seemed routine a few short weeks ago – commuting to work, going to the gym, or gathering with friends – is now either a daunting task or a non-existent option. This shift has impacted our technology, our workforce, and our business environments almost overnight and with minimal warning.