Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Email Security
Organizations Take 43 Hours to Detect an Spear Phishing Cyber Attack
New data makes it crystal clear that spear phishing is a real problem… and organizations may not properly be prepared to detect and address it. Cybercriminals know the more targeted a phishing attack – from the email theming to the impersonation to the intended victim – the more likely the attack will be a success.
What to do after a business email compromise (BEC) attack
A business email compromise (BEC) attack involves cybercriminals making use of phishing to defraud an organization of funds. BEC is a highly devastating and costly cyberattack and has resulted in $26bn in losses since July 2016, with little to no recovery options available.
MailMarshal: Delivering Cloud Based and On-Premise Security Peace of Mind Against Advanced Email Threats
The recent discovery of a zero-day vulnerability in a well-known email security product further underscores the importance of robust email security that can effectively counter advanced email threats, offer a defense-in-depth approach, and operate in the cloud or on-premises. To start, if you believe you have suffered a breach, Trustwave’s Digital Forensics and Incident Response (DFIR) is ready and online to take your call and start helping your organization recover. Click here.
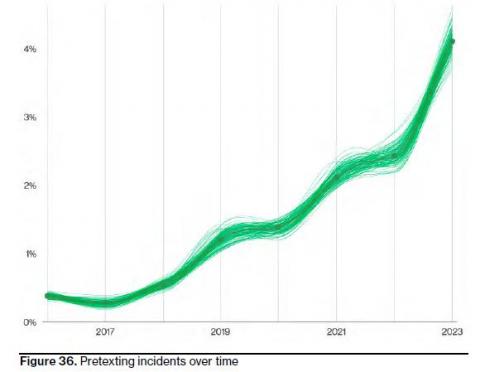
Verizon: Pretexting Now Tops Phishing in Social Engineering Attacks
The New Verizon DBIR is a treasure trove of data. As we covered here, and here, people are one of the most common factors contributing to successful data breaches. Let’s drill down a bit more in the Social Engineering section. They explained: "Now, who has received an email or a direct message on social media from a friend or family member who desperately needs money? Probably fewer of you. This is social engineering (pretexting specifically) and it takes more skill.
Why Companies Have Great Success Training Employees With Simulated Phishing Tests
We occasionally learn of articles and papers that claim that security awareness training and/or simulated phishing campaigns are not effective. We don’t want to disparage what these individuals have found in their own experience, and we encourage everyone to find out how various social engineering mitigations work for themselves and their environments.
Verizon: Email Reigns Supreme as Initial Attack Vector for Ransomware Attacks
My analysis of this year’s newly-released Verizon Data Breach Investigations Report begins with ransomware findings that point back to users as a big problem. If you only read one report each year to give you an idea of what’s going on with cyber attacks, it’s Verizon’s Data Breach Investigations Report (DBIR). Each year, analysts sort through tens of thousands of data breach incidents (some successful, some not) and identify the attack patterns.
Smishing Campaign Expands to the Middle East
A Chinese-speaking phishing gang has expanded its targeting from the Asia-Pacific region to the Middle East, researchers at Group-IB have found. The gang, which the researchers call “PostalFurious,” impersonated a toll operator and a postal service in the Middle East.
North Korean Phishing Campaign Targeting Think Tanks, Academics and Media
The U.S. and South Korean governments have issued a joint advisory outlining a North Korean phishing campaign, The Register reports. The threat actor, known as “Kimsuky,” is targeting “individuals employed by research centers and think tanks, academic institutions, and news media organizations.”
What is whaling?
Enhancements to network security within organizations have made it harder for threat actors to penetrate networks and systems. As a result, people have become the primary target for cyberattacks, with email providing the most effective mechanism for launching these attacks. This leads to all employees within an organization being frequently targeted by phishing attacks.