Adventures in monitoring a hostile network: Black Hat Europe 2024
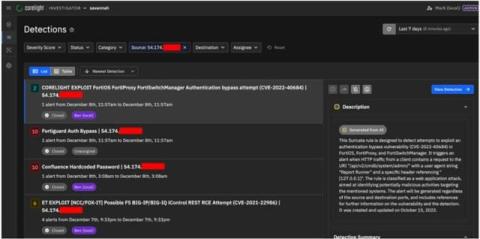
Working in the network operating center (NOC) at Black Hat Europe, we’re never quite sure what we’re going to see. The anxiousness I feel there is similar to what I’d experience when I was blue-teaming for a corporate network. I could prepare all I wanted, read all the blogs about the current threat trends people and companies were tracking on the Internet, and review all the red team and vulnerability scanner reports to identify likely targets.