Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
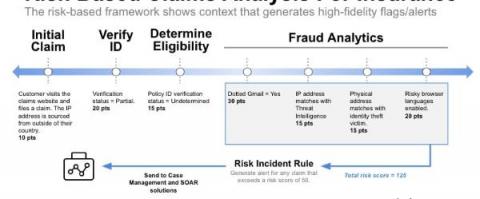
How to choose a CRQ framework
To get a handle on increased cybersecurity threats, businesses need to know what’s at stake. If you don’t know what you’re defending and what the implications of a cyber event could be, then it’s hard to make cybersecurity decisions. For example, you could be spending time and money on cybersecurity awareness training while your biggest vulnerabilities stem from third-party exposure.
Framing the Modern Conversation Around Digital Transformation and Digital Risk
Following my recent AISA session about security transformation in October, I am digging further into the value that can come from both security and digital transformation, applying security service edge capabilities and zero trust principles as part of the broader digital transformation strategy.. In the first part of this three-part blog series, I am going to take a look at how an understanding of digital strategy and digital risk are foundational to a modern security transformation journey.
Mobile Device Forensics: Challenges, Threats, & Solutions
Mobile forensics is the process of accessing, recovering, and analyzing digital evidence from mobile devices using a court accepted methodology. The information that can be gleaned from a criminal’s phone is highly valuable. That’s why mobile forensics and digital forensics as a whole are valuable assets for law enforcement and intelligence agencies worldwide.
Diagnosing Board Reporting and Its Challenges
Three-quarters of U.S. CEOs in PwC’s 24th Annual Global CEO Survey said they are “extremely concerned” about cyber threats. They want to understand roadblocks, cyber insurance coverages, and budget allocation, among other critical topics. CISOs prefer the language of technology, and boards prefer the language of finance.
Russian-Speaking Threat Actors Claim New DDoS Attacks Against U.S. Targets
Citing senior Cybersecurity and Infrastructure Security Agency (CISA) officials, journalistsreported on November 8 that DDoS attacks had temporarily disabled the website of a state government. A group claiming to be pro-Russian hacktivists, CyberArmyofRussia_Reborn, claimed responsibility for that attack and another on the website of a U.S. political party’s governing body on the same day, specifying one target IP address for each organization.
Reputational Risk Mitigation
Simplify your procurement process and subscribe to Splunk Cloud via the AWS marketplace Unlock the secrets of machine data with our new guide All companies want to protect their reputation as any mishandling of it, either self-inflicted or via outside forces, can have a devastating impact. Mitigating reputational issues involves mitigating the risk that leads to them.
The Future of Digital Forensics: Challenges & Opportunities
With the rise in cybercrime, including malware and ransomware attacks, digital forensics has become vital for many organizations. Digital forensics is the science of recovering, investigating, and analyzing digital records, often called digital artifacts, or in legal language forensic artifacts. This can be to find evidence of a crime, but is more often used to identify activity occurring on a computer and to understand how a cyberattack or breach may have occurred.
SecurityScorecard Enables Cyber Insurers to Shift from Static to Dynamic Loss Control
It’s no secret that loss control programs are essential for cyber insurance. Unlike other forms of insurance where the risk and assets don’t change much during a policy term, cyber insurance is meant to mitigate a constantly evolving risk and cover organizations whose security posture is always changing. A cyber insurance policy could be priced completely differently today compared to a few weeks or months later.
FTX, risk management, and attack surfaces - Visibility is the Key
The FTX crypto disaster is a great lesson in risk management. It brings into focus the importance of knowing where your valuables are and how they are being managed.