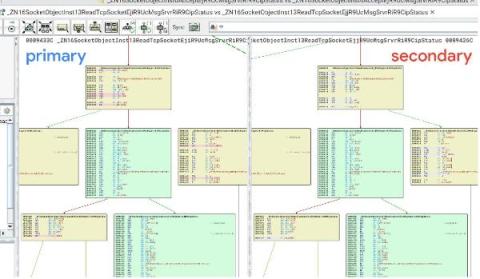
Department of Justice disrupts Moobot botnet commandeered by Russian APT28: analysis of attacks against routers and malware samples
On February 15, the US Department of Justice announced “Operation Dying Ember”: the takedown of a botnet controlled by APT28, the Russian military cyber threat actor also known as Fancy Bear. APT28 was previously known for developing the VPNFilter botnet, which targeted routers and network attached storage devices and was also disrupted by the DoJ in 2018.