Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
February 2023
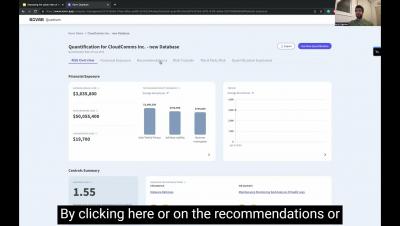
New Feature: NIST CSF Mitigation Recommendations
Does your organization currently speak in the NIST framework language? Say bye-bye to manual mapping and say HELLO to filling out inputs in the NIST CSF framework. This new release helps security teams better align with the organization’s internal communications around security controls. We know that staying consistent with the company’s terminology can better help you achieve your goals.
January Cyber Roundup
T-Mobile has once again fallen victim to a massive new cybersecurity breach, discovered on Jan. 5. The company has a history of hacks from recent years, for which it was fined hundreds of millions of dollars. Using weak API security, the attack caused the exposure of the personal data of more than 37 million customer accounts, which was apparently first accessed on or around Nov. 25. The stolen records include addresses, phone numbers and dates of birth.
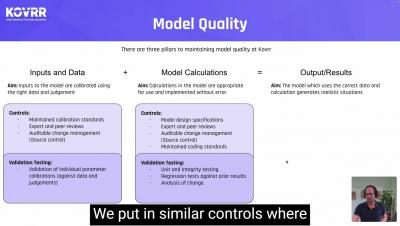
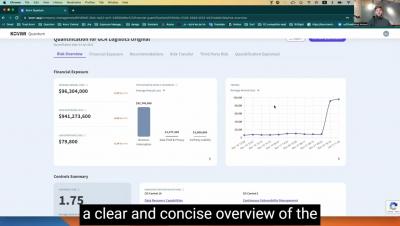
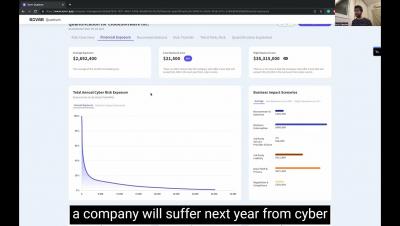
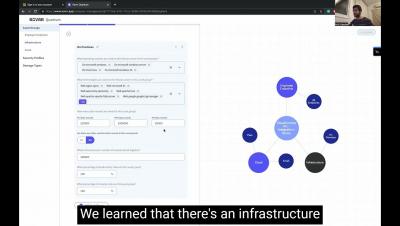
Importance of Insurance-Validated Risk Models to Quantify Cyber Risk
By its nature, cyber risk is dynamic. New events happen and evolve all the time, making it difficult for enterprises to financially quantify their financial exposure to cyber attacks. Around two years ago, for example, distributed denial-of-service (DDoS) attacks were making headlines, and now ransomware has come into heightened focus. It's reasonable to believe that other types of attacks will emerge in another two years and continue to change thereafter.
2022 seems to be on target for the lowest year of reported breaches by large US corporations
The number of data breaches reported in the first 6 months of 2022 has put this year on track to be the lowest year of reports in the last 5 years for large US corporations. By looking at the rate at which data breach events have been reported so far this year, we predict that the number of events reported is expected to be 15-20% of the number of breaches reported in 2021
Why Hackers Love Credentials: Parsing Verizon's 2022 Breach Report
The 2022 Verizon Data Breach Investigations Report (DBIR), the fifteenth such report in as many years, leads off with a startling statistic: Credentials are the number one overall attack vector hackers use in data breaches. Use of stolen credentials accounts for nearly half the breaches studied by Verizon, far ahead of phishing and exploit vulnerabilities, which account for 19% and 8% of attacks, respectively. Botnets, the fourth most common entry path for hackers, represent a mere 1% of attacks.
Ask A Ciso Series: Part 3 - How should CISOs prepare themselves for 2023 challenges?
If you missed the first two parts of our series, we strongly suggest you visit the links here and here.