SecOps In Seconds: Prioritizing Incidents for Investigation in Splunk Mission Control
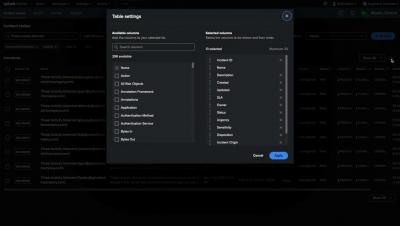
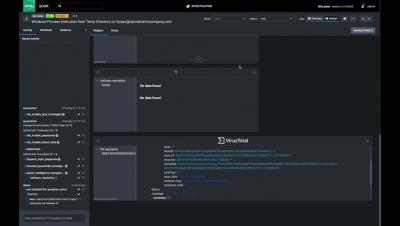
This short video takes you through the basics of using Mission Control's Incident Review feature to prioritize your incident investigations. Product Manager Matt Sayar will show you the ropes and help you navigate this feature so you can better understand how to deploy it yourself.