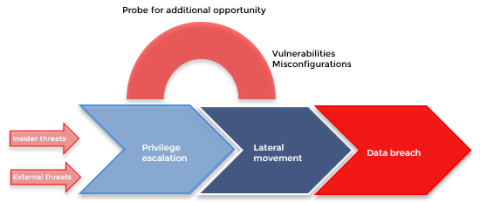
Understanding how attackers move inside your organization
Cyberthreats have been coming at us from the left, right, and center. The number of cyberattacks is forever on the rise, and companies need to keep ramping up their security measures to protect themselves. It’s important that these measures cover every aspect of a network environment. To understand why monitoring your whole environment is so important, let’s take a look at what an attacker might do once they get inside your organization.