Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
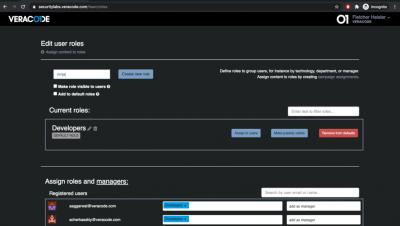
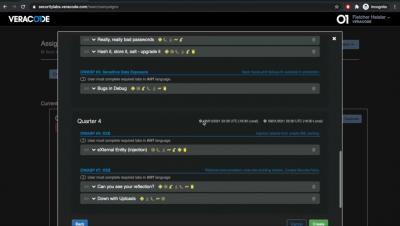
Create a Campaign and Assign Content to Roles in Security Labs
Create Users Within Veracode Security Labs or by Using Your Company SSO
SAST, DAST, SCA: What's best for application security testing?
With a 43% rise in data breaches tied to web application vulnerabilities according to Verizon, enterprise security teams are looking more closely at how security controls can be integrated to DevOps without impacting productivity. But with so many automated security testing tools (SAST, DAST, SCA) on the market, it’s important to understand the difference and when to use them to ensure robust Application Security.
Top 5 Most Powerful IoT Security Testing Tools
The network of interconnecting devices to exchange data popularly known as the Internet of Things is evolving rapidly in the fast-paced industry of technology. However, advancement in IoT has also taken a toll on security. IoT Systems strive to enhance productivity, efficiency, and flexibility but also invite uncalled risks to the network. IoT Security stands as the need of the hour for secure and holistic development.
Rego Unit Testing
This post is going to outline some basics, interesting tidbits and caveats on unit testing Rego policies.
Automated Security Testing for Developers
Today, more than ever before, development organizations are focusing their efforts on reducing the amount of time it takes to develop and deliver software applications. While this increase in velocity provides significant benefits for the end users and the business, it does complicate the process for testing and verifying the function and security of a release.
Create and Manage API Service Accounts with the Identity API
Red Team Assessments - The Fundamentals 1.3
The final part of this mini Red Team blog series discusses the benefits a Red Team Assessment will bring to your organisation. A security test of any sort is ultimately designed to see how your business can mitigate and learn from any issues found. Yes, compliance can come into this and passing and failing a test is a factor but creating a strong infrastructure to protect the business and customer interests is the key factor here.
Red Teaming - The Fundamentals 1.2
In part one we discussed what a Red Team Assessment is, but how does a Red Team Assessment differ from a Penetration Test? With a Red Team Assessment, we’re testing the whole company, essentially how it fares up to a worst-case scenario attack, whether that’s by a competitive company engaging in corporate espionage hell-bent on disrupting business, or harvesting data, or a criminal organisation breaking in and stealing physical equipment or damaging key infrastructure.