Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Effective Unit Testing for Java Applications: Common Challenges and Solutions | Code Intelligence
How to Find Bugs In Java at Scale With CI Fuzz CLI and JUnit | Code Intelligence
New Features and Enhancements Coming to the Tanium User Experience
My takeaways from Converge 2022 and preview of what’s to come with Tanium UX in the future.
The importance of back up and DR
Where would your business be without its data? As the building blocks of any organisation, data is unquestionably integral. Hence why making sure it’s backed up properly should be an essential part of any company’s business continuity plan. At Stripe OLT, we often talk about the loss of data from a cyber-security perspective, however it’s also important to recognise that data loss is also caused by hardware failure and human error.
Malicious Macros Adapt to Use Microsoft Publisher to Push Ekipa RAT
After Microsoft announced this year that macros from the Internet will be blocked by default in Office, many threat actors have switched to different file types such as Windows Shortcut (LNK), ISO or ZIP files, to distribute their malware. Nevertheless, Office documents are still actively leveraged in many campaigns and pose a large risk to organizations, especially with threat actors continuously finding new ways to avoid detection.
Top bug bounty platforms for organizations to improve security
As mentioned in Wikipedia: “A bug bounty program is a deal offered by many websites, organizations and software developers by which individuals can receive recognition and compensation for reporting bugs, especially those pertaining to security exploits and vulnerabilities”. For instance, Company ‘A’ wants to audit/test it’s apps i.e., web & mobile apps for security vulnerabilities & bugs, it will have two options.
10 Questions to Help You Choose the Right Log Management Solution
A good log management solution powers observability for security, engineering, IT and compliance teams. But with so many options available, how do you choose the right one? When evaluating potential log management solutions, start by asking these 10 questions to find the right balance of security, performance and value based on your requirements — and to reveal any limitations that could potentially hold you back.
CVE-2022-47633: Kyverno's container image signature verification can be bypassed by a malicious registry or proxy
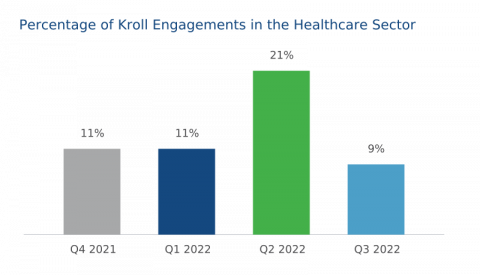
Cyber Threat Intelligence Series: A Lens on the Healthcare Sector
A review of recent Kroll incident response cases consistently proves that the healthcare industry is one of the most frequently targeted sectors. This observation mirrors what is experienced by national cybersecurity agencies as multiple warnings have been launched during 2022, highlighting how ransomware gangs and nation state actors are now aggressively targeting healthcare institutions.