Securing and Accelerating Public Sector Networks with Cloudflare Magic WAN
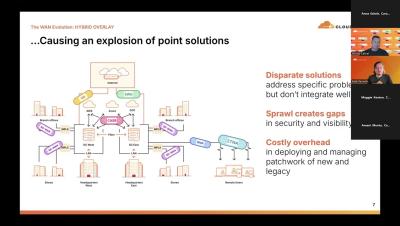
Cloudflare's Magic WAN is a secure, global network service that connects enterprise locations and users with faster, more reliable performance. It replaces traditional VPNs and MPLS with a cost-effective solution, leveraging Cloudflare's extensive edge network to improve both speed and security. In this webinar, you will learn how to: Seamlessly integrate Magic WAN with Cloudflare’s security features Enhance protection against modern network threats Optimize network traffic for better performance Reduce costs compared to traditional VPNs and MPLS solutions.