The Key To Detecting AI Threats - CTRLtheThreat Cybersecurity Tips From Cato CTRL
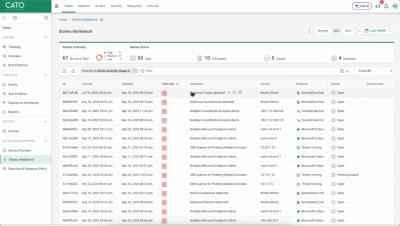
The key to detecting AI threats? Detecting them before they detect you. Tune in to this week's series in which Dolev Attiya, threat researcher and member of Cato CTRL, shares insights about AI malware threats, agent to agent and top ways to stay protected. Subscribe: short.url/aBcXyZ Let’s connect: Instagram: short.url/aBcXyZ LinkedIn: short.url/aBcXyZ X (Twitter): short.url/aBcXyZ TikTok: short.url/aBcXyZ.