SASE in China: Secure, Reliable Connectivity
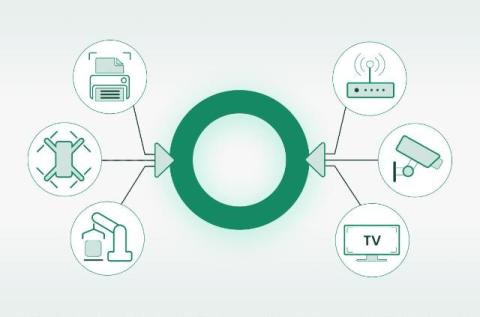
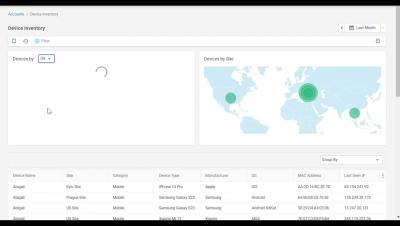
China is a vital market for global enterprises but often poses connectivity challenges due to strict regulations, unpredictable network performance, and complex compliance requirements. But what if you could turn these challenges into opportunities? Join Philip Walley as he introduces Cato SASE, the ultimate solution for seamless, secure, and high-performance global connectivity to and from China.