Strengthen Your Cyber Insurance Position: Why Proactive API Security is Key
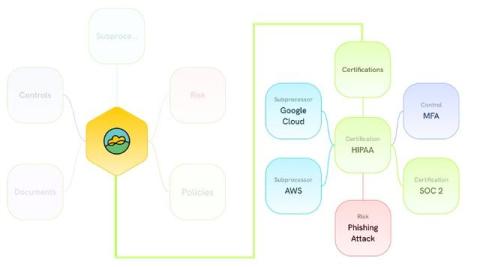
Navigating the cyber insurance market in 2025 feels tougher than ever. Premiums are rising, requirements are stricter, and underwriters are scrutinizing security controls with unprecedented detail. While you're likely focused on endpoint security, MFA, and backups, are you overlooking a critical attack surface that insurers increasingly care about?