Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
(SBOM) Creation of your Software Bill of Materials
Generating an SBOM is just the tip of the iceberg
It has been nearly a year since the President Biden’s Executive Order 14028 catapulted Software Bills of Materials (SBOMs) from niche topic to the forefront of efforts to improve security of cyber supply chains. Since then not only have federal agencies including NIST and CISA delivered significant amounts of guidance and insight, but SBOMs have been the subject of intense debate across developer communities and beyond.
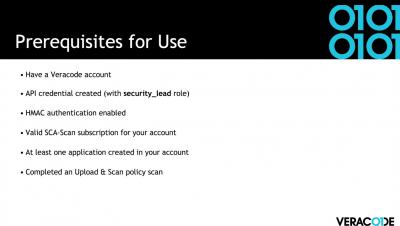
How to generate a Software Bill of Materials (SBOM) using Veracode Software Composition Analysis
How to Generate an SBOM in Veracode SCA
Emerging government regulations have driven the advancement of standards for securing software supply chains. The production of a Software Bill of Materials (SBOM) in a standard format is an increasing audit and compliance need for large organizations.
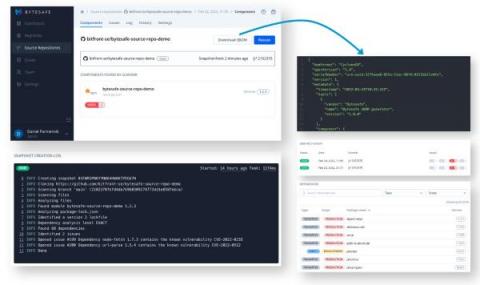
Export and Distribute SBOMs Directly From Your Git Repositories
Guest Blog by Daniel Parmenvik – CEO of bytesafe.dev For many, Software Bill of Materials (SBOMs) have changed from a manual list of assets for due diligence procedures to become an integral and automated part of software development. The ever increasing appetite for open-source software translates into a need to keep track of software assets (or open-source dependencies) for all applications, at any given point in time.
With SBOMs, Sharing is Caring
Thanks to President Biden’s Executive Order on Cybersecurity (14028) last May, Software Bills of Material (SBOMs) are now discussed by developers, security and deployment teams and even boards of businesses around the world. These “ingredients” lists for software are mandated for those selling to US Federal government and are quickly becoming an expected element of any software implementation. Rightly so.
RKVST Set Free
Today we make RKVST available for public use with a free access tier so you can discover what a Zero Trust Fabric can do for you. From tracking software supply chain lifecycles to nuclear waste, RKVST is a powerful tool that builds trust in multi-party processes, when it’s critical to have high assurance in data for confident decisions. But before going all the way you can start simple: tracking software releases and contents with SBOMs.
Build a software bill of materials (SBOM) for open source supply chain security
More than ever, developers are building web applications on the foundations of open source software libraries. However, while those libraries make up the software bill of materials (SBOM) components inventory, not all developers and business stakeholders understand the significant impact on open source supply chain security that stems from including 3rd party libraries.
Introducing the RefBOM for SBOM
Since President Biden’s Executive Order last spring, the industry has been racing to define, standardise and now produce SBOMs to describe the hundreds of thousands of software products sold to and used by federal government and beyond. So far, little thought has been given to the management of SBOMs in practice. Finding the right SBOMs for all the software an organisation relies upon can already feel like hunting for needles in haystacks.