Claude Code converts threat reports into LimaCharlie detection rules #cybersecurity #ai
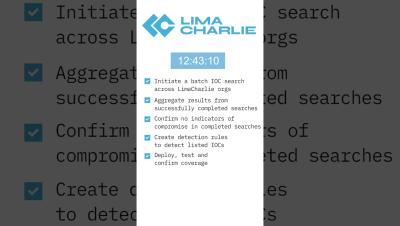
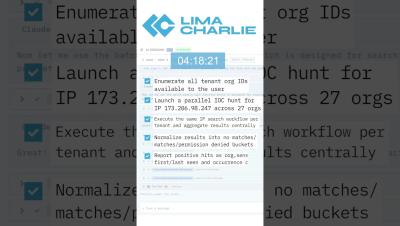
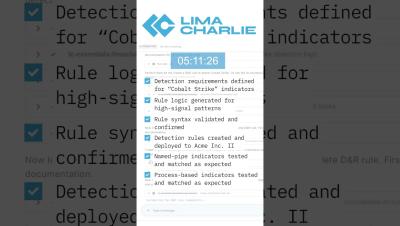
Feed Claude Code a threat report URL and it'll search for compromise indicators across LimaCharlie tenants, confirm the environment is clean, then it'll create and deploy detection rules. The agent extracts IOCs, generates rule logic, validates through testing, and establishes continuous monitoring. Security teams can operationalize published threat intelligence without manual rule writing.