Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability Management: The Beginner's Guide
As available software on the market increases, so do vulnerabilities. When a company's system is weak due to vulnerabilities in the software it uses, attackers take advantage of the situation to: This, in turn, causes the company to lose customers, reputation and money. To reduce threats, network personnel and system administrators are always on the front line, constantly patching the organization's software and operating systems. But to what end?
The Future of Security Operations Centers
Earlier this year, Splunk sponsored the report, "SOC 2025: The Future of Security Operations Centers" from Securosis, which is based on previously published blogs by analyst and president Mike Rothman (now with Techstrong Research).
How Homomorphic Encryption Works & When To Use It
Homomorphic encryption brings a whole new paradigm to encrypting data. In this article, I’ll explain homomorphic encryption, including.
Six SIEM Essentials for Successful SOCs
A few weeks ago, Gartner named Splunk Enterprise Security a Leader in the 2022 Gartner® Magic Quadrant™ for SIEM. This is the ninth consecutive year that Splunk has been placed in the Leader’s quadrant. We’re honored to be recognized and we believe our placement is a testament to our commitment to delivering a data-centric security analytics solution that accelerates threat detection and investigations.
The people have spoken and Splunk wins twice at the ITAwards
You know that us Splunkers love to go deep into use cases and figure out what helps our customers the most. However in today’s business world, industry recognition goes a long way in proving the value in the products and services we use. For example if you were Munich Airport, then it would speak volumes to others if your airport was named as a “First Five-Star Airport” or if you were Dachser Logistics and went on to win the “One Eaton Supplier Premier Award”.
Coffee Talk with SURGe: DOJ China Espionage, Drizly Complaint, Text4Shell, U.S. Midterm Elections
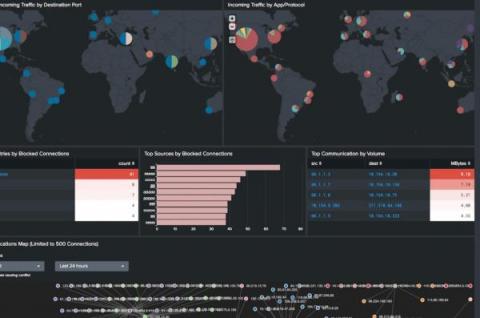
Splunk Security with the Infosec App
There's so much that can be accomplished with Splunk’s security tools. Today, we are going to focus on all the benefits of the InfoSec App for Splunk. The InfoSec app — which is an entitlement to Splunk customers — is powered by the Splunk platform, and relies on accelerated data models and the Common Information Model (CIM) to provide a consistent and normalized view into the event data that you’ll bring into Splunk.
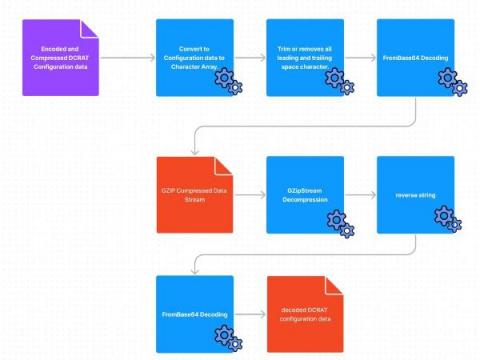
Dark Crystal RAT Agent Deep Dive
The Splunk Threat Research Team (STRT) analyzed and developed Splunk analytics for this RAT to help defenders identify signs of compromise within their networks. Remote Access Trojans (RATs) are one of the most common tools used by threat actors as a malicious payload to attack targeted hosts and steal information. One example is the Dark Crystal RAT (DCRat) that is capable of remote access, post exploitation and data exfiltration.