Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Secure Bots and Service Account Access With Ephemeral Certificates
"Create cryptographically secure access keys" and "Rotate keys frequently" — These are probably the best security recommendations one can get for bot authentication security. In reality, while these are good practices, they simply aren't enough. First, cryptographically secure keys only prevent simple guessable or brute-force attacks, but the impact is catastrophic if the keys themselves are stolen.
How to get a shell in a Kubernetes Pod
Containers are used for packaging software and all its dependencies before deployment. Before the era of containers, software developers had to deal with compatibility issues during deployment. These could occur when software functions properly during the development phase but fails to function due to dependency issues in the production environment. With containers, however, all the software dependencies used for development can be shipped and used in the production environment.
How to Secure Amazon RDS Access With an Identity-Aware Access Proxy
Databases are sensitive resources that need an additional layer of protection and security. Though database servers have built-in authentication and authorization mechanisms, they are not designed for cloud-based, multi-tenant access mechanisms. Managed databases such as Amazon RDS are accessed and administered by different personas with varying levels of access permissions.
Teleport Raises $110 Million Series C at $1.1 Billion Valuation
I have news to share. Teleport has just secured $110M in Series C funding to keep growing the business that I started with my co-founders Sasha Klizhentas and Taylor Wakefield in 2015. This is exciting for founders and employees, but I think it is also excellent news for all software engineers who are crying out for a better way to manage secure access to their mission-critical cloud infrastructure. More on that below.
How to enable WebAuthn based second-factor authentication in Teleport.
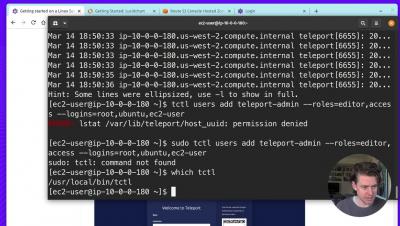
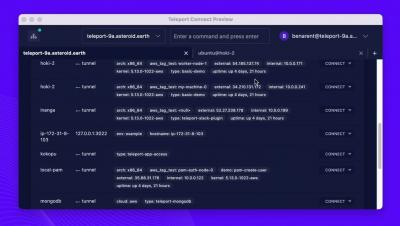
Getting started with Teleport 9
0:00 Introduction
1:10 Install Teleport on Root Cluster
5:33 DNS
6:36 Configure Teleport
10:17 Create Teleport User
14:09 Have Fun with Teleport
SSH configuration: ssh_config
This blog post covers some of my favorite settings for configuring the behavior of an ssh client (i.e. what is in the man pages for ssh_config). Whether you are looking to add some additional security constraints, minimize failures, or prevent carpal tunnel, ssh_config is an often underutilized, yet powerful tool. While the examples in this article focus on ssh configurations on unix based systems like linux and macOS, running an ssh server on windows is supported using openSSH.
KubeCon EU 2022. Why you need Teleport in your Kubernetes Infrastructure
Every Kubernetes developer’s favorite time of year is just around the corner, Kubecon EU 2022! Whether you’re attending in person in beautiful Valencia, Spain, or watching the conference from your couch at home, here are a few reasons why — if you operate any Kubernetes infrastructure — you need Teleport.