Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
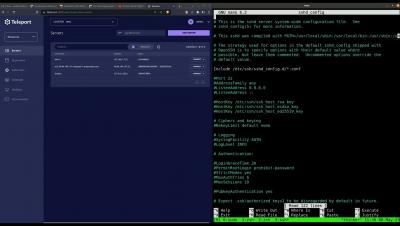
Quickly onboard engineers and protect infrastructure with Teleport as a SAML and IDP
In this episode, we’ll go over how companies protect access to applications using Teleport. This webinar will focus on the workflow for quickly onboarding engineers to access your infrastructure and highlight how teams can use Teleport as a SAML and IDP for apps and websites. In the latter half of the session, we'll delve deeper into the technical intricacies of SAML and share valuable tips for enhancing the security and modernization of your IDP through the implementation of passwordless authentication. Don't miss this opportunity to bolster your organization's access security with Teleport.
Login with Teleport. Teleport as a SAML Identity Provider
Starting with Teleport 12.1, Teleport Enterprise teams can now use Teleport as a SAML SSO identity provider. This feature allows teams to use Teleport to authenticate to external services, thereby letting teams use SAML SSO to login to external SaaS apps and internal applications that support SAML. Let’s look at a few examples.
Introduction to Teleport
Want to know how Teleport's Access Platform technology replaces VPNs, shared credentials, and legacy privileged access management technologies, improving security and engineering productivity? Watch this session from Phil and Alex to learn more about Teleport's Certificate Authority and Access Platform for your infrastructure.
Multi-layered Zero Trust with Yash Kosaraju
For this 18th episode of Access Control Podcast, a podcast providing practical security advice for startups, Developer Relations Manager at Teleport Ben Arent chats with Yash Kosaraju. Yash is Chief Security Officer at @Sendbird Sendbird's mission is to build connections in a digital world, providing APIs and services for chat products with API and tools to integrate into apps. This episode dives into how teams can build multi-layered security systems to go beyond zero-trust to let teams do their work but also provide checks.
Going Beyond Network Perimeter Security by Adopting Device Trust
It’s a familiar nightmare you’ve heard of and might even face as a developer or security engineer: alerts firing in all directions warning that your company’s VPN and firewall — that supposedly “safe” defensive perimeter around your infrastructure — has been breached. And the scariest part is that you find out after the fact — after access credentials and customer assets have been stolen.
Overview of Teleport 12: Device Trust and Desktop Access
Join us as we showcase the latest features of Teleport, the first identity-native infrastructure access platform for engineers and machines. Teleport delivers phishing-proof zero trust for every engineer and service connected to your global infrastructure by replacing insecure secrets with true identity.
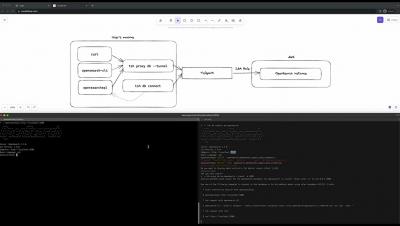
Getting Started With Teleport 12 | Kubernetes Edition
In this video, we'll look at how to connect a Kubernetes cluster to Teleport. We'll also look at a new "pod-level RBAC" feature released with Teleport 12.
Securely Deploy Kubernetes Clusters with Teleport Machine ID and GitHub Actions
Current approaches to managing machine identity for infrastructure like Kubernetes Clusters and CI/CD workflows rely on outdated security mechanisms like passwords, shared secrets, and other manual processes that are error prone and increase the risk of breach.