Teleport Workload Identity with SPIFFE: Achieving Zero Trust in Modern Infrastructure
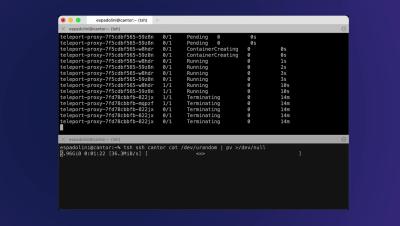
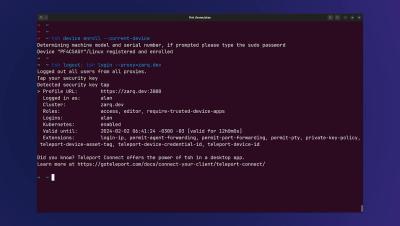
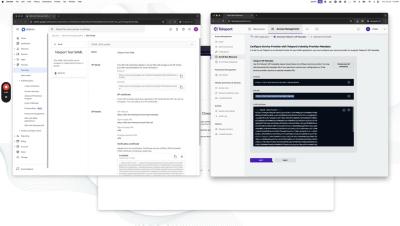
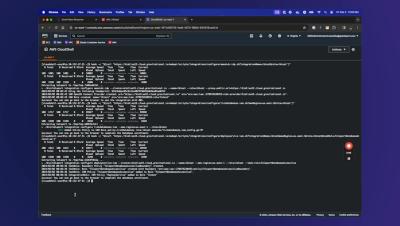
Teleport Access Platform generates cryptographic identity for users, machines, devices, and resources, creating a single source of truth for what users and machines are accessing what in your modern infrastructure. Now, engineers will be able to generate identity specific to workloads and services, enabling your full modern infrastructure stack to operate with zero trust authentication.