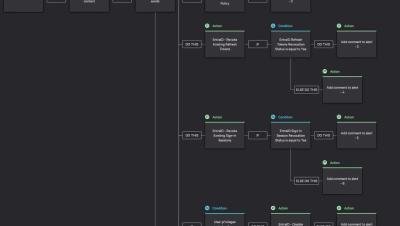
CrowdStrike Falcon Next-Gen SIEM Unveils Advanced Detection of Ransomware Targeting VMware ESXi Environments
CrowdStrike Falcon Next-Gen SIEM, the definitive AI-native platform for detecting, investigating and hunting down threats, enables advanced detection of ransomware targeting VMware ESXi environments. CrowdStrike has observed numerous eCrime actors exploiting ESXi infrastructure to encrypt virtual machine volumes from the hypervisor to deploy ransomware in organizations. Access to ESXi infrastructure typically takes place as part of lateral movement.