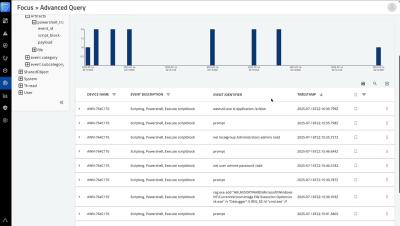
What is Advanced Endpoint Protection
Endpoints play a vital role in any organization’s operations. However, endpoints are susceptible to a variety of cyber attacks, particularly malware and ransomware – threats that remain highly popular among threat actors. Additionally, many social engineering attacks seek to gain access to individual users’ endpoints.