Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Phishing Scams Have Reached New Heights: How to Improve Detection and Response
The Anti-Phishing Working Group (APWG) Phishing Activity Trends Report reveals that in Q2 of 2022 there were 1,097,811 total phishing attacks. This marks the worst quarter for phishing observed to date, exceeding Q1 of 2022 which was the first time the three-month total exceeded one million.
Outpost24 supports TIBER-EU for threat intelligence-based ethical red-teaming
TIBER-EU is the European framework for threat intelligence-based ethical red-teaming and the first EU-wide guide on how authorities, threat intelligence and red-team providers should collaborate with different organizations to help improve their cyber resilience. Thanks to its threat intelligence offering, Outpost24 is well-positioned to create attack scenarios in line with the TIBER-EU framework.
Good Password Hygiene Mitigates Personal and Business Cyber Risk
In our previous Cyber Security Awareness Month (CSAM) blog we talked about the added value we as cybersecurity practitioners can bring to the table by sharing knowledge we take for granted with individuals across the organization that will ultimately help strengthen defenses. The first topic we covered was multi-factor authentication (MFA). CSAM’s next topic is using strong passwords. Here are a few tips we have found useful to share with colleagues, as well as family and friends.
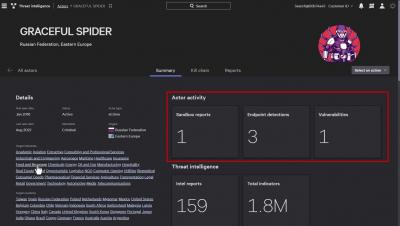
Threat Intelligence 101
Elastic Wins 2022 CyberSecurity Breakthrough Award for Threat Intelligence Platform of the Year
Help Enable Smarter Decisions During Cybersecurity Awareness Month
Do a quick search for the top cybersecurity breaches thus far in 2022 and you’ll quickly be overwhelmed with reports of cryptocurrency thefts, attacks targeting multinational corporations and critical infrastructure, and nation-state backed attacks spurred by ongoing geopolitical conflict. It’s easy for individuals to let their guard down and think they’re safe because these complex attacks aren’t targeting them specifically.
Strategies for Gathering and Contextualizing Cyber Threat Intelligence
In my previous blog, I covered the many different types of cyber threat intelligence and why gathering CTI is beneficial to security teams. In this post, I will dig into the cyber threat intelligence lifecycle framework and a model to help correlate and contextualize your findings.
CrowdStrike Store - Falcon Intelligence
Unlock the Power of Automation: Vulnerability Management
We’ve spoken extensively about the importance of taking a data-driven approach to Vulnerability Management. In short the efficiency and effectiveness of vulnerability management processes depend heavily on inclusion of threat intelligence for both prioritization and response activities. At any given time, only a small fraction of existing vulnerabilities are actively exploited or exploitable.