Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How Sysdig is Using the ThreatQ Platform to Enhance Cloud Threat Detection and Response
It is always interesting to learn about real-world examples of technologies at work. So, when ThreatQuotient invited me to share how we at Sysdig are using the ThreatQ Platform to enhance our cloud detection and response solutions, I was happy to participate.
Combining Artificial Intelligence with Threat Intelligence
One of the primary challenges that our security analysts encounter is where and how to best use their time. Monitoring and reviewing the constant influx of data and alerts produced by our client’s networks whilst also finding the time to keep on top of trending and emerging threats is no mean feat, and not particularly conducive to a healthy work-life balance…
Budget and momentum are key to cybersecurity automation maturity - and CISOs are feeling left behind
As cyber threats intensify and the human and financial resources available to deal with them remain limited, there is a growing need for automation in cybersecurity. The intelligent automation of key cybersecurity processes can significantly improve an organization’s posture and at the same time support under-pressure employees by reducing reliance on manual processes.
Budget and momentum are key to cybersecurity automation maturity - and CISOs are feeling left behind
As cyber threats intensify and the human and financial resources available to deal with them remain limited, there is a growing need for automation in cybersecurity. The intelligent automation of key cybersecurity processes can significantly improve an organization’s posture and at the same time support under-pressure employees by reducing reliance on manual processes.
ThreatQuotient Publishes 2022 State of Cybersecurity Automation Adoption Research Report
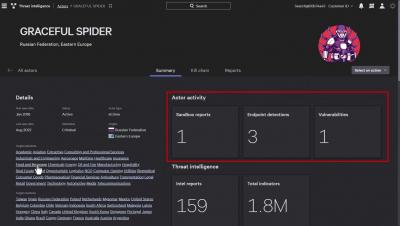
How to Defend Against Threats with Falcon Intelligence
TIPs to Measure your CTI Program
Nowadays, organizations are exposed to a high volume of security related information. Unfortunately, most of these organizations have little to no capabilities of using this information in a proactive manner, i.e. using information to try to change or anticipate an outcome. In other words, using information to produce intelligence products. It is safe to say that few of these organizations have a clear understanding of what Cyber Threat Intelligence (CTI) is and what it is not.
How Banks Around the World Can Prevent Cyber Attacks
As both consumer and commercial banking clients shift to primarily utilize online banking, they still have high expectations that their financial assets will be secure. In 2021, the banking industry reported 703 cyberattack attempts per week — a 53% increase from 2020. And the cost of cyberattacks in the industry has reached $18.3 million annually per breach.
Wrapping up CSAM 2022 with Vulnerability Management Advice for Everyone
As we wrap up Cybersecurity Awareness Month (CSAM) 2022, the final topic we’ll cover is updating software and patching vulnerabilities. According to the 2022 Data Breach Investigations Report (DBIR) from Verizon one of the top paths threat actors use to infiltrate organizations is exploiting vulnerabilities. And there appears to be no end in sight as the number of unique security vulnerabilities rose almost 10% in 2021, up to 20,142 from 18,351 in 2020.