Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Mastering Python virtual environments: A complete guide to venv, Docker, and securing your code
Python, as a versatile and widely used programming language, has an extensive ecosystem of modules and packages. As you navigate this ecosystem, it's important to understand the role of virtual environments. In this article, we will delve into what virtual environments are, why developers need them, and some common tools for creating Python virtual environments.
How to choose a security tool for your AI-generated code
“Not another AI tool!” Yes, we hear you. Nevertheless, AI is here to stay and generative AI coding tools, in particular, are causing a headache for security leaders. We discussed why recently in our Why you need a security companion for AI-generated code post. Purchasing a new security tool to secure generative AI code is a weighty consideration. It needs to serve both the needs of your security team and those of your developers, and it needs to have a roadmap to avoid obsolescence.
Build and deploy a Node.js security scanning API to Platformatic Cloud
In this guide, we'll dive into the powerful combination of Platformatic and Fastify, unlocking rapid backend development with an emphasis on robustness and security. Whether you're a seasoned Node.js developer or just starting out, this article is a helpful start to enhancing your familiarity with Node.js PaaS environments such as Platformatic.
Krampus delivers an end-of-year Struts vulnerability
On December 20, 2023, NIST updated a CVE to reflect a new path traversal vulnerability in struts-core. This is CVE-2023-50164, also listed on the Snyk Vulnerability database, with 9.8 critical severity CVSS. If you’ve been doing cybersecurity long enough, you remember the 2017 Equifax breach, which also took place due to an unpatched Struts vulnerability. In this post, I outline the issue, discuss its severity, walk you through a proof-of-concept exploit, and provide remediation advice.
Kroger's approach to supply chain security
Recently, Snyk hosted a wine tasting & customer discussion featuring David Imhoff, Product Security Leader at Kroger. The discussion focused on tackling the challenges of securing digital supply chains. Kroger is a retail giant with 2,700 stores and 400,000 employees. The organization faces unique challenges because it operates on such a massive scale, adding complexity to its software supply chain and security.
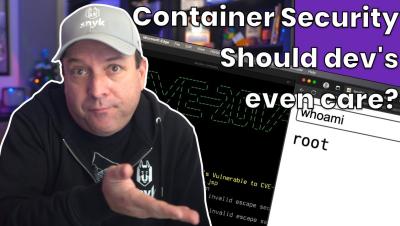
Why should developers care about container security?
How to prevent open redirect vulnerabilities in Laravel
An open redirect vulnerability occurs when a website allows user-supplied input to influence the destination of a redirect without implementing proper validation or sanitization measures. To exploit this vulnerability, an attacker may send users a seemingly trustworthy link, which, when clicked, redirects them to a harmful website, potentially leading to phishing attacks or other malicious activities.
Command injection in Python: examples and prevention
Despite Python's reputation for simplicity and versatility, ensuring the security of Python programs can be challenging if you or other team members neglect security best practices during development. Additionally, you’ll likely use libraries or other open source projects while building a Python application. However, these resources can introduce additional security issues that leave your program vulnerable to exploits such as command injection.
Is your team on the *security* naughty or nice list?
As kids, many of us felt anticipation, excitement, and maybe even nervousness during the holiday season. Had we been good enough to get the Gameboy, Barbie Dream House, or Etch a Sketch we’d been pining for, or were we just going to get a big ol’ lump of coal?