Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
New years resolution: Don't show my security tokens when hacking my demo application on stage
Traditionally, we start the new year with resolutions. We want to do more good things, like working, other things we try to eliminate. Considering the latter, my 2022 resolution is to stop accidentally exposing confidential information while I hack my application during demos on stage or similar. Yes, this new years resolution sounds very specific, and it has an excellent security horror story behind it…
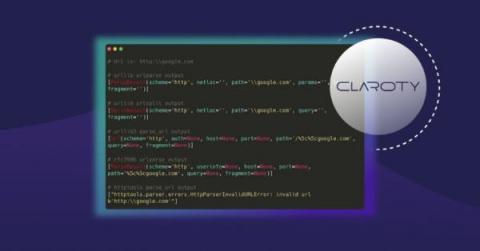
URL confusion vulnerabilities in the wild: Exploring parser inconsistencies
URLs have forever changed the way we interact with computers. Conceptualized in 1992 and defined in 1994, the Uniform Resource Locator (URL) continues to be a critical component of the internet, allowing people to navigate the web via descriptive, human-understandable addresses. But with the need for human readability came the need for breaking them into machine-usable components; this is handled with URL parsers.
Open source maintainer pulls the plug on npm packages colors and faker, now what?
On January 8, 2022, the open source maintainer of the wildly popular npm package colors, published colors@1.4.1 and colors@1.4.44-liberty-2 in which they intentionally introduced an offending commit that adds an infinite loop to the source code. The infinite loop is triggered and executed immediately upon initialization of the package’s source code, and would result in a Denial of Service (DoS) to any Node.js server using it.
FTC highlights the importance of securing Log4j and software supply chain
Earlier this week, the FTC issued a warning to companies regarding the Log4j vulnerability. Given the rampant exploitation of the recently discovered vulnerabilities in this ubiquitous open source logging package, it’s encouraging to see the agency take this rare step, beginning to form a firm stance on software supply chain security. Although this increased scrutiny from the FTC may at first seem daunting, violations can be remediated with the right practices.
The Missing Pieces in Securing your SDLC
Demystifying DevOps-Pros, cons, dos & don'ts
CTF secrets revealed: TopLang challenge from SnykCon 2021 explained
If you attended SnykCon 2021, you may remember our inaugural CTF: Fetch the Flag. In this CTF, TopLang was a web challenge of medium difficulty that we received a lot of positive feedback about. So for those of you that loved it, this write-up explains how our team internally approached tackling and solving this challenge. This challenge was a pretty typical example of what is known as an “oracle attack” using blind SQL injection.
Developer security resolutions for 2022
As 2022 begins, it’s a great time to set resolutions for the coming year. Don’t worry, we don’t expect you to become a CrossFit guru or break world records on your Peloton. Instead, how about you set goals to improve your abilities as a secure developer? All too often, we choose resolutions that set ourselves up for failure. A better approach is to set realistic goals.
New workshop for securing a DevOps pipeline with Snyk, Bitbucket, and AWS
Development teams are frequently under the gun to deliver software quickly, which is difficult to do without modern tools to build, test, and deploy applications efficiently. That’s why Atlassian’s Bitbucket Cloud — a Git-based source code repository service in the cloud that streamlines software development for collaborative teams — was built for both speed and efficiency. The challenge nearly all organizations face is ensuring development speed and security at the same time.