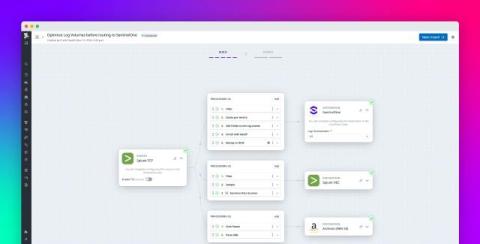
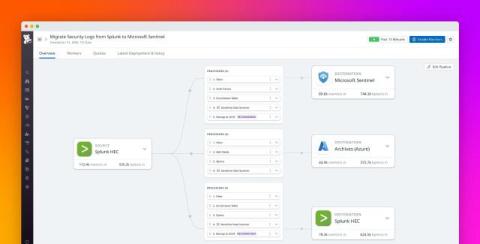
Using LimaCharlie as an Observability Pipeline to reduce SIEM storage costs
LimaCharlie's SecOps Cloud Platform (SCP) creates a scalable, versatile, and actionable observability pipeline by collecting and standardizing telemetry from the full security stack. Stream data from any input, route it to any output. The SCP provides visibility into telemetry sources and empowers users to create automated responses to actionable events in the pipeline.