Evasive Phishing Campaign Steals Cloud Credentials Using Cloudflare R2 and Turnstile
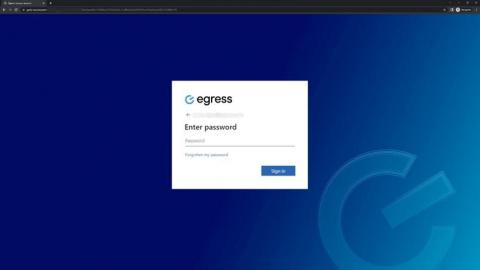
From February to July 2023, Netskope Threat Labs has been tracking a staggering 61-fold increase in traffic to phishing pages hosted in Cloudflare R2. The majority of the phishing campaigns target Microsoft login credentials, although there are some pages targeting Adobe, Dropbox, and other cloud apps. The attacks have been targeting victims mainly in North America and Asia, across different segments, led by the technology, financial services, and banking sectors.