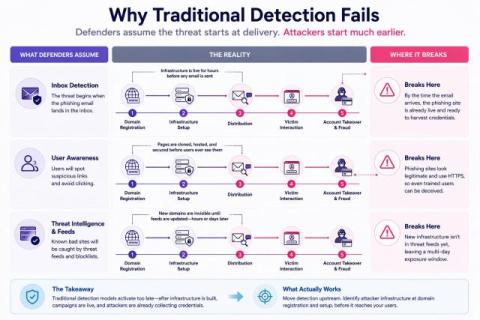
How to Detect Phishing Before It Happens: Moving Beyond User Awareness
By the time a phishing email lands in an inbox, the attacker’s infrastructure has already been live for hours. That’s not a hypothetical. Zimperium’s 2024 research found that 60% of newly created phishing domains receive a TLS certificate within the first two hours of registration. The site is credentialed, hosted, and ready before most security teams have any signal it exists.