Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Strengthening Resilience Through MITRE ATT&CK
Using a Ransomware Assessment to Identify Gaps & Risks
Breaking Down the Complexity with Cloud Through BAS
Welcome & Keynote: Increasing Attack Surface for FSIs
Into the future: what might cybersecurity look like in 2023?
How can Cyber Security Playbooks and Runbooks Benefit Your Security Program?
You probably don’t need anyone to tell you that, today, infosec and cybersecurity are challenging and fast-paced endeavors. In the last five years alone, we’ve seen a myriad of industry altering developments — from an ever expanding universe of privacy compliance legislation and the permanent entrenchment of hybrid and remote work, to growth in the size and scope of data breaches — the world of security has proven ever complex and ever-shifting.
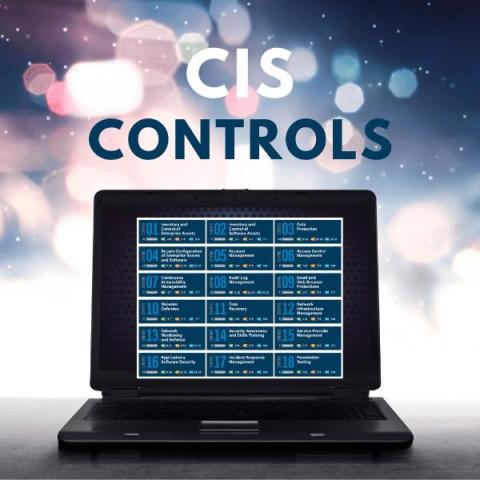
What Are CIS Benchmarks (Guide For 2023)
There are numerous CIS benchmarks which provide system administrators and other IT technicians with configuration baselines and best practices across the various levels of different CIS criteria to allow them to secure the configuration of any systems and devices they use within an organisation. Here we will provide you with a detailed overview of what CIS benchmarks and controls should mean to you, along with useful references for further reading where needed, as part of this guide.
Cybersecurity challenges facing SMBs and steps to protect them
Businesses come in many different sizes, yet, they all share one similarity; the growing need for cybersecurity in today’s ever-changing technology landscape. While large companies with robust security infrastructure and experience may ward off many aspiring cybercriminals, small to medium-sized businesses (SMBs) prove to be ideal targets.