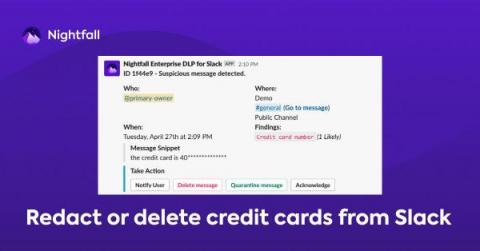
How to Prevent Credit Card Number Exposure in Slack for PCI Compliance
For many companies, a business credit card is part of the organization’s lifeblood. As such access to it must be vigilantly maintained. One potential area of risk is employees sharing credit card details in collaborative SaaS applications like Slack, where these details are at significant risk of being exposed to unauthorized parties.