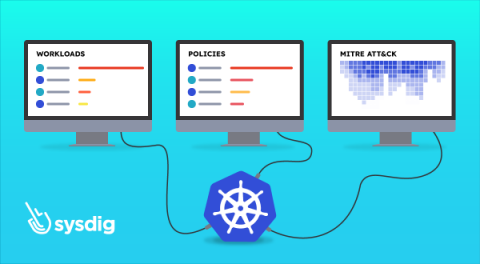
Respond Instantly to Kubernetes Threats with Sysdig Live
Discover how Sysdig Secure’s new “Kubernetes Live” informs of your Kubernetes security posture at a glance. Investigating a security incident may be a tennis match. Sometimes, you find yourself jumping from one window to another: one place for runtime events, another one for vulnerabilities, another one for logs. Gathering and correlating all the information available can be a time consuming task, but it’s the only way of having a clear view of what is going on.