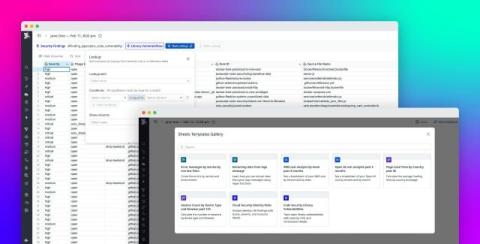
Generate audit-ready vulnerability and compliance reports with Datadog Sheets
Security teams are frequently asked to provide clear, time-bounded evidence of their organization’s security posture. Whether the request comes from external auditors validating SOC 2, ISO 27001, PCI DSS, or internal governance reviews, they typically require collecting vulnerability data from multiple tools, reconciling resource lists, and manually generating spreadsheets for auditors. This process is slow, error-prone, and difficult to repeat consistently.