Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Work from Anywhere (WFA)
Forescout - Security is a Journey Shared
Improving accuracy and value: Why Inviting Vendors is important
As most of our customers know, every single company – customer or not – gets free and unlimited access to their own company’s Scorecard. This view allows them to see the complete details of their scorecard and a high-level view of five other scorecards. SecurityScorecard provides this free access because we know that when companies engage with their scorecard, their scores improve, their attribution becomes more accurate, and our customers lower their own cyber risk.
Exploring 3 types of directory traversal vulnerabilities in C/C++
Directory traversal vulnerabilities (also known as path traversal vulnerabilities) allow bad actors to gain access to folders that they shouldn’t have access to. In this post, we are going to take a look how directory traversal vulnerabilities work on web servers written on C/C++, as well as how to prevent them.
TechBites - Penetration Testing For Businesses
Charts - Sankey
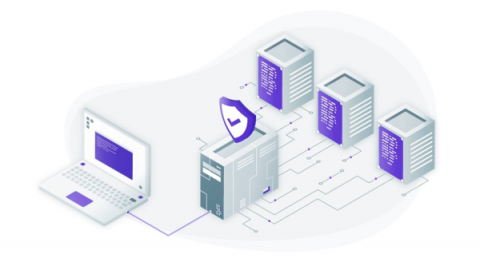
Setting Up an SSH Bastion Host
What is an SSH bastion and how is this different from an SSH jump server or an SSH proxy? In this post, we’ll answer this question and will show you how to set it up using two popular open source projects. Both Teleport and OpenSSH support bastions, and they are extremely similar as they are both single-binary Linux daemons. Both require a simple configuration file usually stored somewhere under /etc/.
What is the difference between client side and server side and why is it important to your everyday security?
For individuals not completely immersed in the world of IT and cybersecurity, it can be hard to keep up with the latest terms and acronyms.
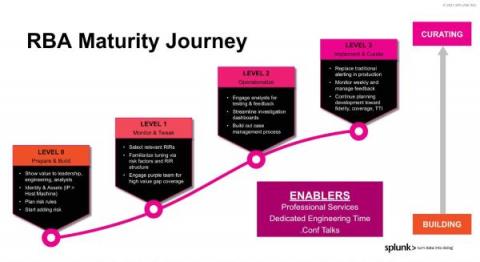
Risk-Based Alerting: The New Frontier for SIEM
If you haven't heard the gospel of risk-based alerting (RBA) in a SIEM context, by the end of this sermon you'll see why you’ll want it running in your environment yesterday, whether you're an analyst, an engineer, or in leadership.